From Integration to Orchestration: Rethinking the Role of Audio in Modern Security Systems
As security environments become more complex, simply integrating systems is no longer enough. This article explores how workflow-driven security and unified communication platforms enable real-time response, better coordination, and more effective operations—highlighting the growing strategic role of audio.

For years, physical security has been dominated by visual data. Cameras, analytics, and video management systems have formed the backbone of most deployments. Yet as environments become more complex—and expectations around response times and operational efficiency increase—there is a growing realization: visibility alone is not enough.
The next evolution of security is not just about seeing more. It’s about understanding more, responding faster, and coordinating better. And this is where integrated audio is starting to play a far more strategic role.
The Integration Paradox
Modern facilities are saturated with technology. Access control systems, video surveillance, intrusion detection, fire alarms, IoT sensors, and analytics platforms all coexist within the same environment. Each system is powerful in isolation, but the real value lies in how well they work together.
For system integrators, this creates both an opportunity and a challenge.
On one hand, integration promises improved situational awareness and operational efficiency. On the other, it introduces complexity—different protocols, proprietary interfaces, and varying levels of interoperability. The result is often a fragmented ecosystem where systems coexist but don’t truly collaborate.
This is what can be called the integration paradox:
the more systems you add, the harder it becomes to create a unified operational picture.
Why Audio Changes the Equation
Audio introduces something fundamentally different to security systems: interaction.
While video helps identify what is happening, audio enables systems to:
- Interpret context beyond visuals
- Trigger immediate responses
- Facilitate real-time human intervention
In essence, audio transforms security from a passive monitoring function into an active engagement layer.
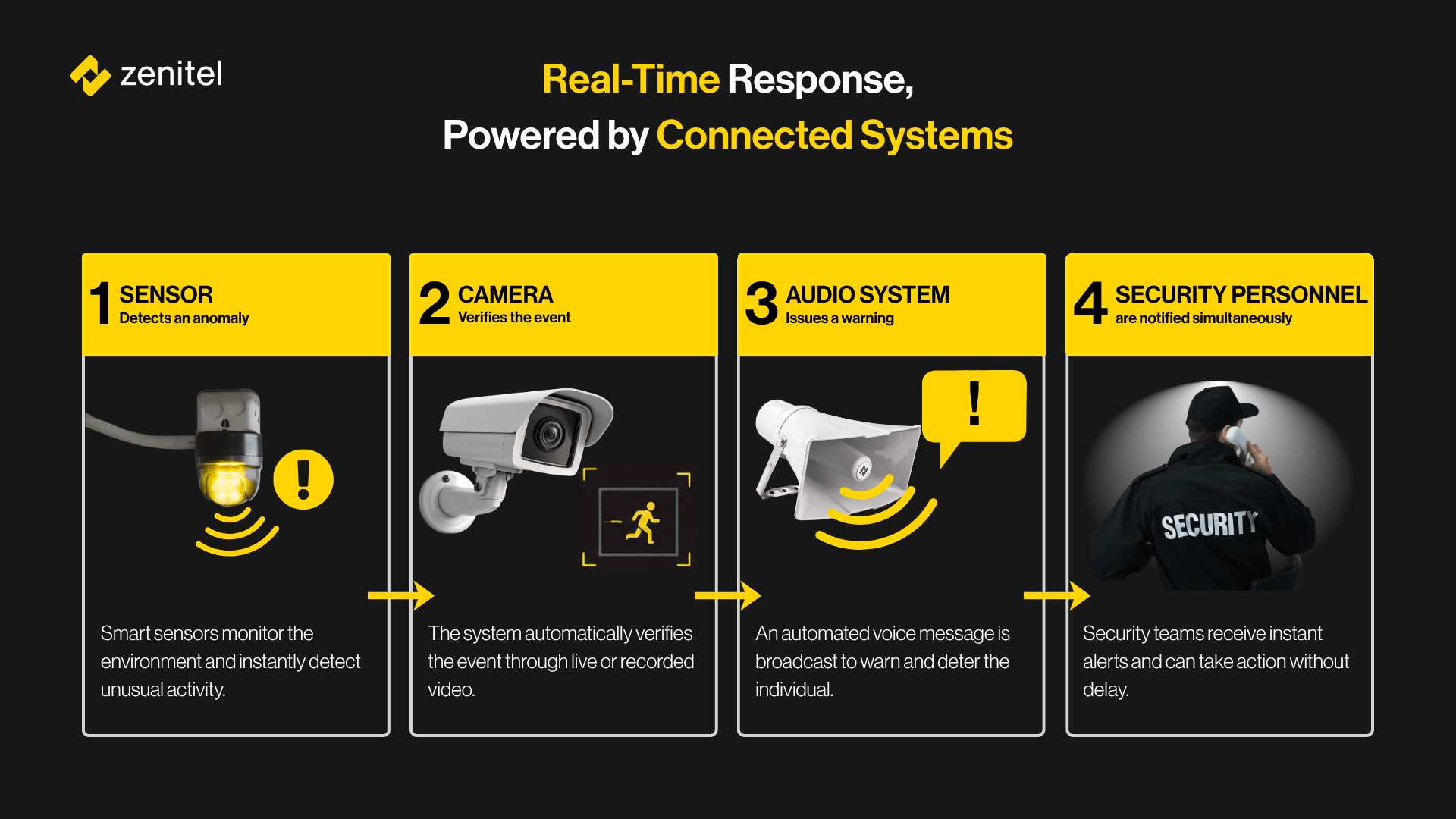
For example, when an incident occurs:
- Video can detect motion or anomalies
- Audio can verify intent (e.g., distress, aggression, or unusual sound patterns)
- More importantly, audio allows operators to intervene instantly—issuing warnings, guiding individuals, or coordinating response teams
This shift—from observation to interaction—is critical in moving from reactive to proactive security.
Levels of Integration: Not All Are Equal
One of the key strategic decisions for integrators is choosing the right level of integration. Not every project requires deep orchestration—but many suffer from under-integration.
Broadly, integration maturity can be viewed in two stages:
1. Device-Level Integration
At the most basic level, audio devices connect directly to platforms like video management systems. This enables capabilities such as:
- Audio monitoring
- Event-triggered playback
- Basic voice communication
While useful, this approach is inherently limited. Communication is often one-directional or constrained, and scalability becomes a concern—especially in larger environments where synchronization and coordination matter.
2. Unified Communication Platforms
The next stage is where integration evolves into orchestration.
Instead of treating audio as an add-on, it becomes a core communication layer that connects:
- Video systems
- Access control
- Public address and voice alarm
- Intercoms and radios
- IoT sensors and analytics
In this model, communication workflows are unified. Events in one system can trigger coordinated actions across others, enabling:
- Real-time collaboration
- Automated responses
- Consistent operational procedures
For integrators, this represents a shift from connecting components to designing end-to-end communication workflows.
The Rise of Workflow-Driven Security
One of the most significant trends shaping modern security architecture is the move toward workflow automation.
Instead of relying solely on operator intervention, systems are increasingly expected to:
- Detect events
- Interpret context
- Trigger predefined actions
This is where integration frameworks and tools—such as API-driven architectures and workflow engines—become essential.
What matters here is not the individual technologies, but how seamlessly they interact. For system integrators, this introduces a new responsibility: designing logic, not just infrastructure.
Balancing Flexibility and Complexity
With increased integration comes increased responsibility. Over-engineering a solution can lead to:
- Higher deployment costs
- Difficult maintenance
- Reduced reliability
The key is to strike the right balance between:
- Depth of integration (how tightly systems are connected)
- Flexibility (how easily workflows can evolve)
- Usability (how operators interact with the system)
This is particularly important as customers demand solutions that can adapt over time. Static integrations are no longer sufficient—systems must be configurable, scalable, and future-ready.
Cybersecurity as a Foundational Layer
As systems become more interconnected, the attack surface expands. Communication platforms, in particular, are critical assets—if compromised, they can expose sensitive data or disrupt emergency response.
This makes cybersecurity not just a feature, but a design principle.
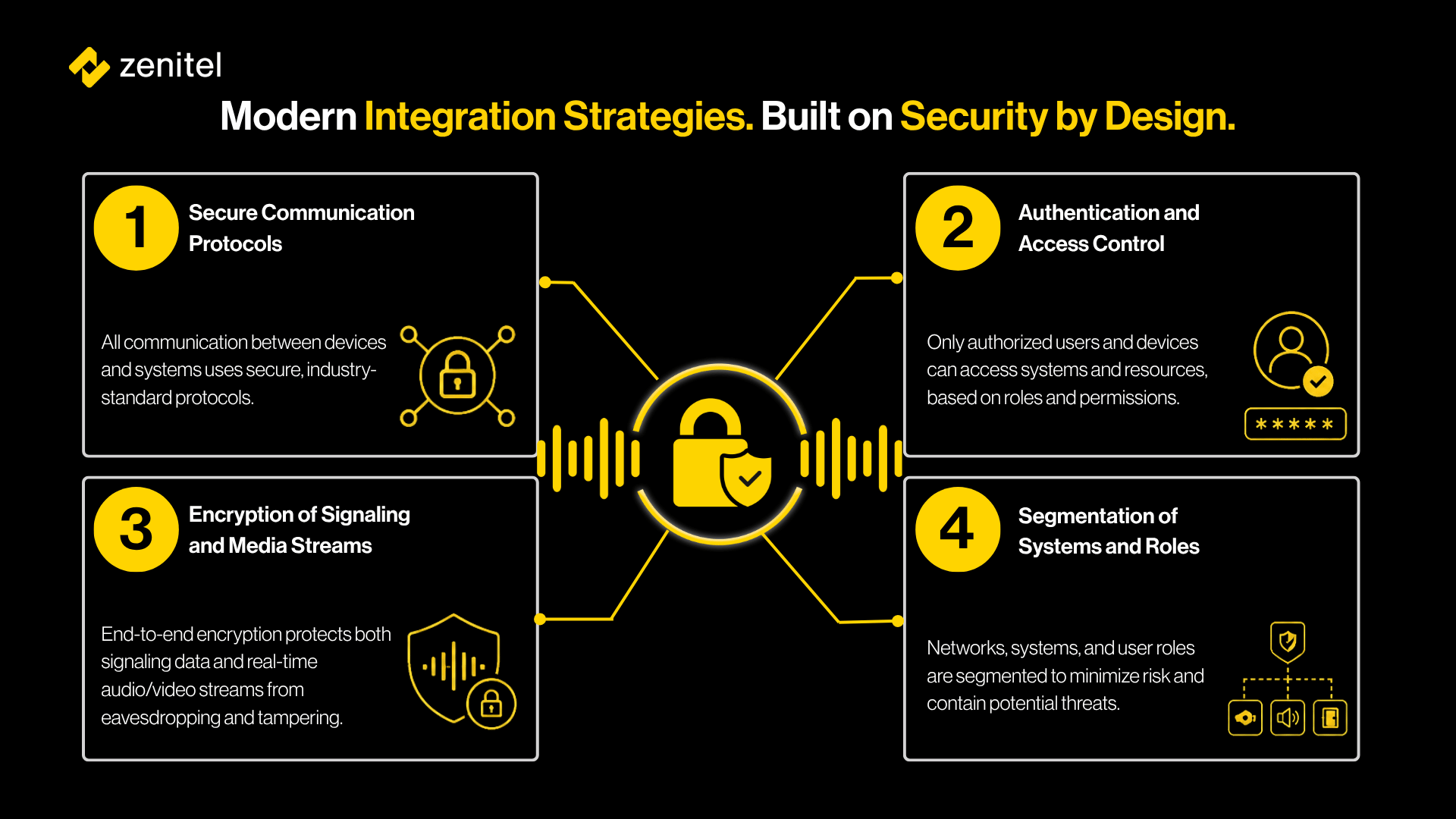
For integrators, this means embedding security into the architecture from day one—not as an afterthought.
A Strategic Shift for System Integrators
The role of the system integrator is evolving.
Traditionally, success was measured by the ability to deploy and connect systems. Today, the expectation is higher.
Customers are looking for partners who can:
- Understand operational workflows
- Design integrated experiences
- Enable proactive and automated responses
- Ensure long-term scalability and security
In this context, audio is no longer just another subsystem. It is becoming a strategic enabler of real-time communication and coordinated action.
Looking Ahead
As the security landscape continues to evolve, the distinction between systems will blur. Video, audio, access control, and analytics will increasingly function as part of a unified ecosystem.
The question is no longer whether systems can be integrated—but how effectively they can be orchestrated.
For system integrators, this presents a clear opportunity: to move beyond integration as a technical task, and embrace it as a strategic discipline.
Because in the end, the value of a security system is not defined by how many technologies it includes—but by how well they work together when it matters most.
